The 2024 Cyber Landscape: Insights and Strategies
In an era where digital threats rapidly evolve, comprehending the cyber threat landscape is crucial for maintaining robust defences. The 2023 report from Recorded Future sheds light on this dynamic field, revealing critical trends and vulnerabilities that pose significant risks to organisations worldwide. This article delves into these insights, offering strategic advice to bolster your cybersecurity measures.
Emerging Threat Dynamics
The past year has been marked by significant cybersecurity incidents, including high-profile exploits of third-party tools such as GoAnywhere, MOVEit, and Citrix NetScaler. These events underscore the complex challenges of managing expanding attack surfaces—challenges compounded by hybrid work environments and increased cloud adoption. Notably, the evolution of ransomware tactics, exemplified by the CL0P ransomware group, calls for an enhanced focus on security vigilance.
“The most notable instances of mass exploitation this year were carried out by the CL0P ransomware group on third-party managed file transfer services, impacting a staggering 2,750 enterprises and approximately 94 million individuals”
The exploitation of vulnerabilities in managed file transfer services by groups like CL0P has had a staggering impact, affecting thousands of enterprises and millions of individuals. These incidents highlight the necessity of rapid response strategies following vulnerability disclosures to mitigate potential damages.
Rapidly update security patches post-disclosure to reduce the window of opportunity for cyber attackers.
Increased Risks from Virtualization and Cloud Migration
Source: The Good, The Bad, and The Vulnerable Report
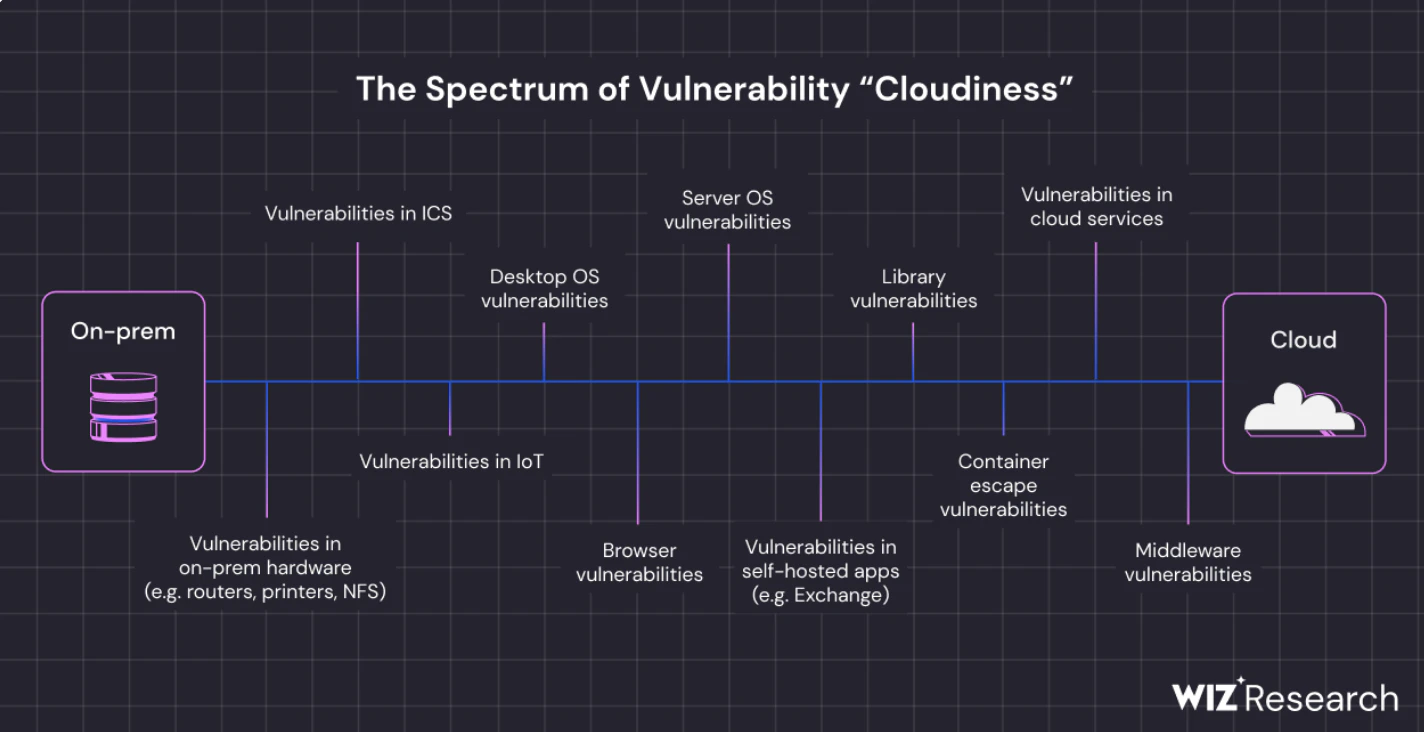
The report also sheds light on the heightened security risks stemming from increased virtualization and cloud migration. The consolidation of cloud services has introduced unique vulnerabilities, often targeted by threat actors aiming to exploit enterprise software and infrastructure. This trend signals a shift in threat actor focus towards high-impact targets that can provide widespread unauthorised access to corporate data and systems.
As we move into 2024, the landscape of cloud security continues to evolve with increasing sophistication. Hybrid and multi-cloud environments are now facing more mature and frequent attacks, which not only threaten sensitive data but also highlight the critical vulnerabilities in systems that were previously considered secure. These environments, due to their complex nature, often become the focal points for new types of cyberattacks.
Furthermore, the reliance on a narrowing supply chain of cloud vendors introduces additional risks. As the number of vendors decreases, the impact of a breach or vulnerability in one of these key players can have far-reaching effects across multiple enterprises. This consolidation of services and vendors necessitates a strategic reevaluation of security protocols, ensuring that organizations are not only defending against known threats but are also preparing for the cascading effects that a single breach can precipitate across their operations.
Vulnerability Commonalities and Preventive Insights
The Recorded Future report identifies two main characteristics common among the exploited vulnerabilities: discoverability via public scans and pre-disclosure exploitation. Surprisingly, most breaches occur post-disclosure, indicating a need for accelerated patching processes. Emphasising foundational security practices such as rigorous patch management, adherence to zero trust principles, and implementation of multi-factor authentication is essential for defending against cyber attacks.
Historical Patterns of Targeting and Strategic Implications
Reflecting on historical cybersecurity incidents, such as the widespread Log4Shell vulnerability, we gain insight into the recurring theme of cybercriminals exploiting high-impact vulnerabilities. This understanding of the implications and the high-value potential of such compromises has been dually noted among threat actors. The Log4Shell incident, among others in previous years, exemplifies the calculated nature of cybercriminal efforts to maximise impact and profit through deliberate targeting. These vulnerabilities, especially those embedded within widely used software components, present an attractive avenue for extensive extortion operations, underscoring the critical need for vigilant and proactive security measures.
This strategic approach to selecting targets reveals a nuanced understanding of the digital ecosystem's interconnectedness and the cascading effects a single vulnerability can have across numerous organisations and sectors. The lesson learnt is clear: cybersecurity is not just about defending against known threats but anticipating the strategic moves of adversaries looking to exploit the fundamental infrastructures that underpin our digital world.
For those looking to deepen their understanding and fortify their defenses, engaging with cybersecurity experts and leveraging cutting-edge threat intelligence solutions can provide the critical edge needed in this relentless battle against cyber threats. Now is the time to act and secure your digital future.
Take the next step in securing your organisation's digital assets and data. Explore our suite of cybersecurity solutions and services designed to empower your business against the threats of tomorrow. Sign up today and join the forefront of cyber resilience.
The fight against cyber threats is relentless, but with informed strategies and proactive measures, businesses can navigate the digital age with confidence.