Business Confidence, Powered by Offensive Security
We find your security gaps and help you close them. Explore our full suite of services and find what’s right for you.
WHY APOLLOSEC?
YOUR SECURITY SPECIALIST PARTNER
At APOLLOSEC, we provide cybersecurity services to businesses of all sizes. From penetration testing and industry-leading vulnerability management, to phishing simulations and tabletop exercises, we help safeguard your digital assets and achieve security compliance.
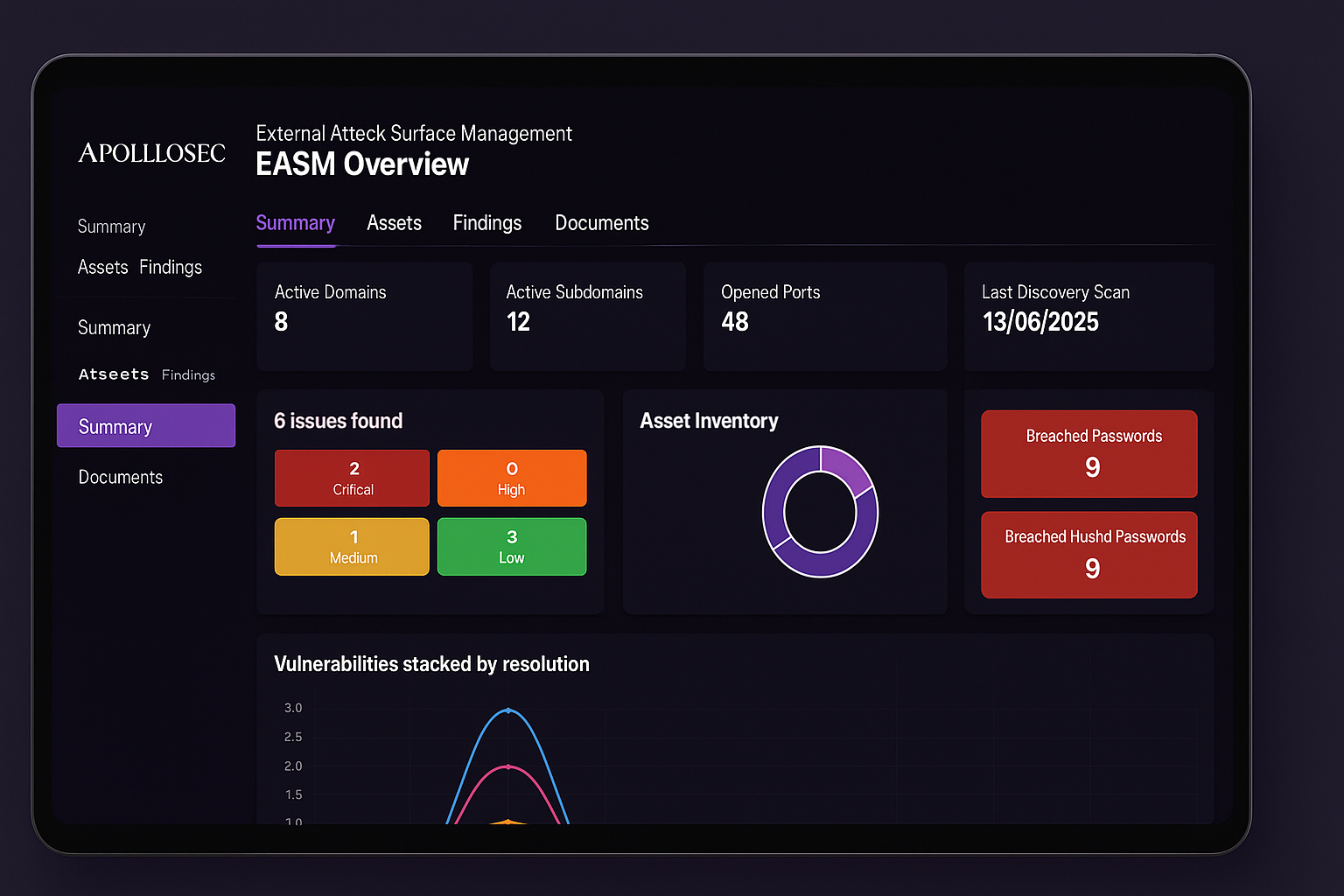
Now, you can leverage our flagship Attack Surface Management (ASM) Platform to identify and track all publicly facing assets. When we discover weaknesses, we’ll alert you immediately, ensuring risks are mitigated before real threats can exploit them. No time wasted spinning up agents. Not limited by scope. Completely externally, just as attackers would be.
The Challenges of Modern Cybersecurity
Understanding the complexities of today's cybersecurity landscape is crucial. Traditional methods are outdated, leaving gaps that sophisticated attackers can exploit.
Traditional yearly penetration tests fail to mimic the sophistication of real-world attackers.
Outdated Testing Models
Modern testing offers only a snapshot of security, not accounting for the dynamic, evolving nature of organisation which adversaries constantly monitor.
Limited in Scope
Common vulnerability scanners often return a high volume of vulnerabilities, masking the few critical exploitable findings.
Ineffective Scanning
The reliance on infrequent and scoped tests gives organisations a misleading assurance, disregarding the evolving risks.
False Sense of Security
Standard tests don’t replicate the sophisticated and persistent techniques used by real-world attackers, overlooking complex attack vectors.
Inadequate Real-World Simulation
What Our Clients Say About US
Our Solution: A Customer Driven Management Platform
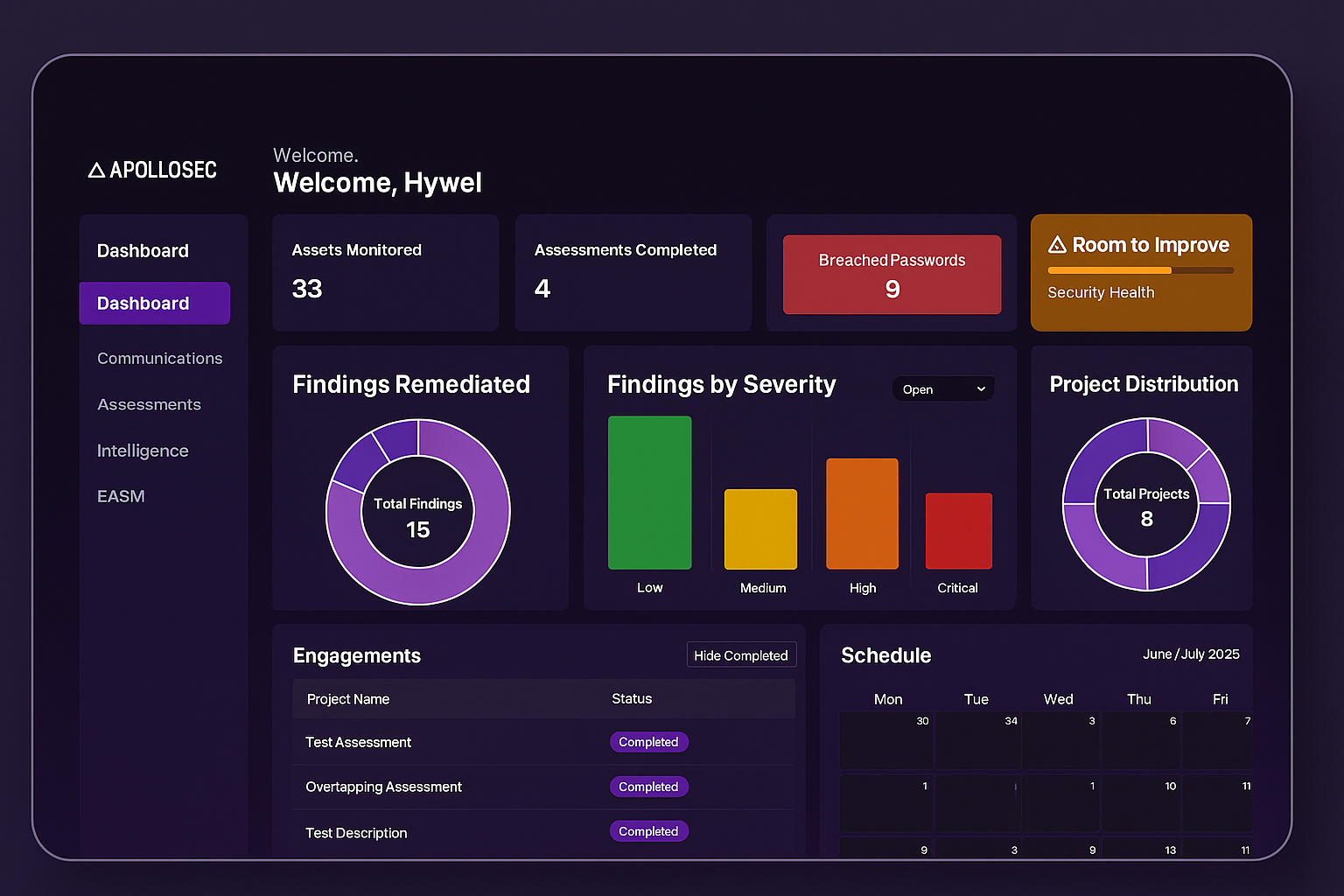
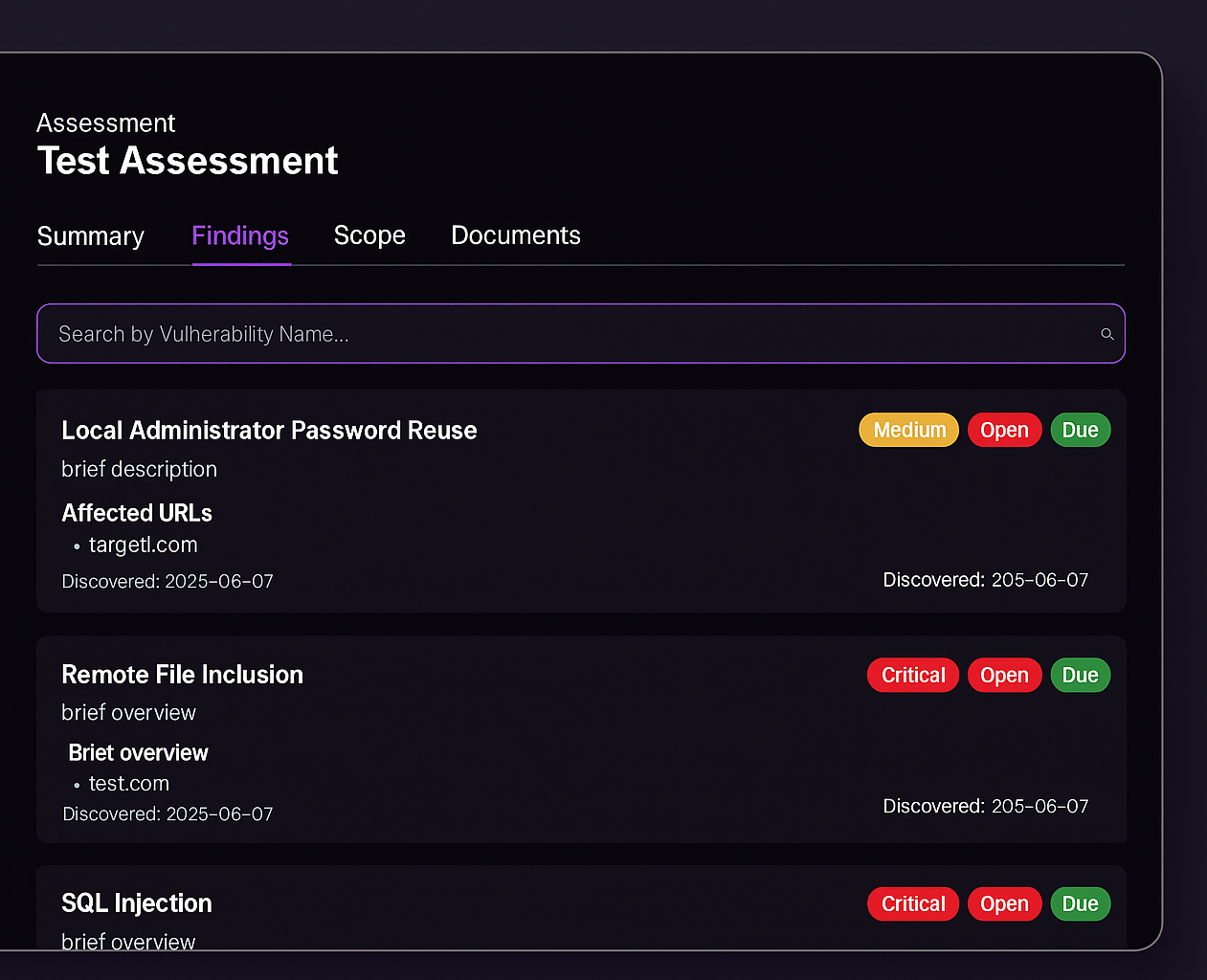
Our penetration testers use our secure online portal to manage assessments from start to finish, delivering detailed findings as soon as they’re available. Reports are written in clear, actionable language so your teams gain the visibility and guidance they need to remediate vulnerabilities quickly and effectively.
Through live reporting, you’ll see each issue the moment it’s discovered—allowing you to prioritize and fix weaknesses before the test wraps up. This continuous, real-time insight dramatically shortens your window of exposure and keeps your attack surface under constant scrutiny.
We Believe in Continuous Improvement
Remediate Issues as They’re Discovered
Our live-reporting dashboard delivers each vulnerability the moment it’s uncovered, so you can start fixing weaknesses immediately—often before the engagement wraps up. This on-the-fly approach accelerates risk reduction and can cut your overall remediation cycle by weeks.
Collaborate Directly with Your Tester
Use the portal’s built-in chat to engage with our technical experts in real time. Get guidance on interpreting findings, advice on best-practice fixes, and hands-on support exactly when you need it.
Continuous Status Tracking
Keep tabs on every finding and asset remediation through our 24/7 portal dashboard. Access up-to-the-minute reports and status updates whenever you need them, ensuring complete visibility and control throughout the testing process.
Always-On Attack Surface Management
Why settle for snapshots when threats are nonstop? Our subscription-based service delivers continuous testing and verification against your entire attack surface—from third-party integrations to cloud workloads. By emulating real-world attackers and adapting to emerging tactics, we uncover and help you shore up critical vulnerabilities in real time. Advanced tooling feeds live insights to your dashboard, empowering you to assess, prioritize, and reinforce defences instantly—so you stay ahead of evolving threats with a truly proactive security posture.
Insights & Stories
Digital Cyber Attacks
Living on The Edge
Insight